Cloud Computing Use is Growing
What exactly is “cloud computing”? Well, the simplest explanation is that it an Internet-based service that provides on-demand access to shared computing resources (e.g., storage, servers, networks, applications, and services) along with data to connected devices. These services allow users to process and store data in the providers’ data centers which are more than likely located some distance away, from across the city to the other side of the world. All of these cloud computing services cost money and typically charge fees based on use.
Supporters of cloud computing say that it simplifies a company’s network infrastructure and reduces upfront costs by replacing servers that would normally be needed to support the business. They also claim that companies can have their applications up and running faster, with lower maintenance and better manageability along with giving their IT departments more flexibility in allocating resources for unstable and erratic demand.
With cloud computing, use can be scaled up and down as computing needs fluctuate. This allows companies to pay for those resources that they use without having to invest in a lot of servers that may or may not be utilized to their full potential all the time. So a lot of companies are asking why pay for internal server capacity, which requires continuous maintenance and resources allocated to it, when they can get the same performance and accessibility at an overall lower cost though cloud computing services?
It’s no wonder that worldwide spending on cloud services is predicted to grow at a 19.4% CAGR from approximately $70 billion in 2015 to an estimated $141 billion by 2019.1 In fact, one of the largest cloud service providers, Amazon Web Services (AWS), reported revenue of $2.4 billion in Q4 of 2015, up 69% over the same period in 2014.1 This data reinforces the expectation that the adoption of cloud-based services is and will continue to increase for the near future.
One of the largest companies offering cloud computing services is the aforementioned AWS, a subsidiary of Amazon.com. They offer a wide variety of cloud services including:
- Compute – virtual servers, containers, 1-click web app deployment, event-driven compute functions, auto scaling, and load balancing
- Storage & Content Delivery – object storage, content delivery network (CDN), block storage, file system storage, archive storage, data transport, and integrated storage
- Database – relational, database migration, NoSQL, cashing, and data warehouse
- Networking – virtual private cloud, direct connections, load balancing, and DNS
- Analytics – business intelligence, data warehouse machine learning, streaming data, Elasticsearch, Hadoop, and data pipelines
- Enterprise Applications – desktop virtualization, email & calendaring, document sharing & feedback
- Mobile Services – mobile development, API management, identity, app testing, mobile analytics, development, and notifications
- Internet of Things – IoT platform, device SDK, registry, device shadows, and rules engine
- Developer Tools – source code management, code deployment, and continuous delivery
- Management Tools – monitoring & logs, resource templates, usage & resource auditing, dev/ops resource management, service catalog, and performance optimization
- Security & Identity – access control, SSL/TLS certificates, key storage & management, identity management, security assessment, and web application firewall
- Application Services – API management, app streaming, search, transcoding, email, notifications, queueing, and workflow
As can be seen above, AWS tries to cover all the cloud computing needs a company may have. All a user needs to do is create an account and sign up for the services that are needed. A variety of tutorials are available on the AWS site to get things up and running fast.
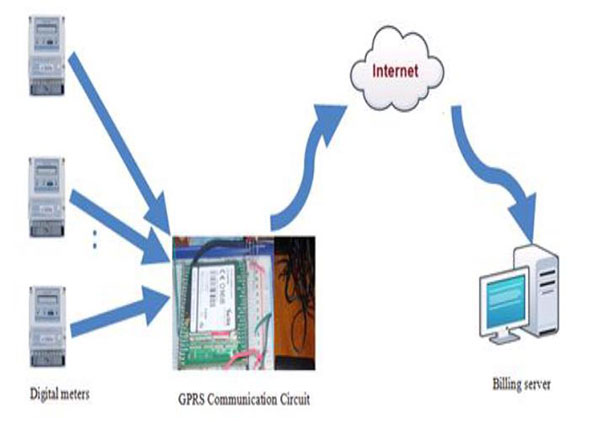
The next thing is getting your devices connected to AWS reliably and securely. With security being a primary concern for companies protecting their intellectual property, developing a secure AWS interface is a primary objective. Microchip has addressed this by offering the zero touch secure development platform.
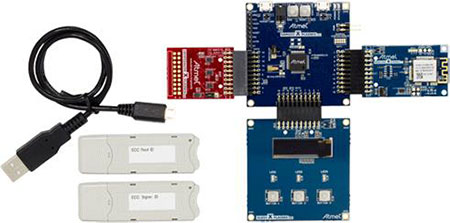 Microchip's Zero Touch Secure Development Platform
Microchip's Zero Touch Secure Development Platform
This is a complete development and prototyping platform for AWS IoT device provisioning. It includes Microsoft’s root module (evaluates certificate root operations prior to engaging a root certificate authority) and signer module (generates signer certificates and registers them to AWS servers as well as provisions IoT devices with unique certificates). The platform demonstrates zero-touch device onboarding by allowing the removal of any user manipulation of keys and certificates to securely connect a device to AWS IoT applications.
With the prospect of cloud computing services becoming more and more of a factor in enterprise IT provisioning, it makes sense to design your interfacing devices to connect to the services in a secure manner to protect proprietary data. Having that secure connection happen with the least amount of design effort is just a bonus.
References:
1 - Roundup Of Cloud Computing Forecasts And Market Estimates, 2016
Have questions or comments? Continue the conversation on TechForum, DigiKey's online community and technical resource.
Visit TechForum